ICYMI: Industrial Operator, Cybersecurity Experts Testify on Rising Threats to Operational Technology
February 9, 2024
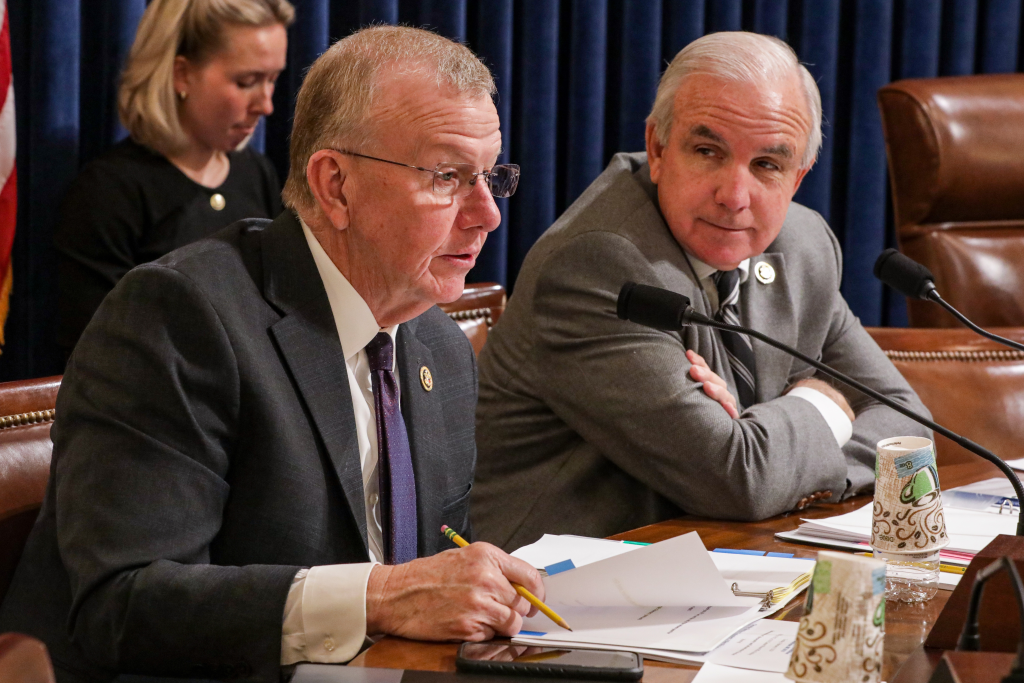
WASHINGTON, D.C. — This week, the House Homeland Security Subcommittee on Cybersecurity and Infrastructure Protection, led by Chairman Andrew Garbarino (R-NY), held a hearing to examine operational technology (OT) security, specifically in the water sector, and the Cybersecurity and Infrastructure Security Agency’s (CISA) role in its implementation and prioritization. Witness testimony was provided by Robert M. Lee, CEO and co-founder of Dragos; Charles Clancy, senior vice president and general manager of MITRE Labs, chief technology officer of MITRE; Kevin Morley, manager of federal relations at American Water Works Association; and Marty Edwards, deputy chief technology officer of OT and internet of things at Tenable.

In his opening statement, Lee explained the risks to operational technology and emphasized the need for an outcomes-based approach to security:
“The cyber threat landscape for OT has shifted irreversibly. More standardized infrastructure has brought efficiencies, a homogenous infrastructure to manage, but it’s also opened the door for reusable, scalable capabilities that can be used across sectors. In 2022, Dragos worked with our partners, as well as closely with the United States government, to identify and analyze a malicious capability called PIPEDREAM. It was the first reusable capability to cause the ability for disruptive as well as destructive capabilities across industrial equipment. This class of capabilities will increase the frequency of high consequence attacks we observe.
“The public and private sectors must work together to secure water security and water sector operational technology. For federal agencies, this means providing clear and consistent guidance to the industry that identifies specific requirements they need to support, such as realistic threat scenarios and opportunities to exercise them. When it comes to regulation, the government must harmonize across frameworks and use an outcome-based approach that defines why they are concerned, what the outcome is that we are driving towards, and leaves the how to the private sector. Or simply stated: give us the requirements, not the answers.”

Chairman Garbarino (R-NY) asked witnesses how to address the cybersecurity workforce gap:
“We’ve learned that a common hurdle in securing OT is having the personnel necessary to prioritize and implement guidance. Small and medium organizations and the federal government alike face challenges in hiring and retaining cybersecurity personnel… specifically amongst OT experts. How can CISA help build baseline OT expertise internally and at each Sector Risk Management Agency?”
Clancy answered:
“Zooming out to the macro perspective, we have a huge cybersecurity workforce gap in the country. I think something like 37 percent of cyber vacancies nationwide are unfilled. There are, I think, 300,000 empty cyber jobs. We just don’t have the cyber workforce capacity writ large across the country.
“There’s very few university programs that have any focus on OT, particularly industrial control systems. That just does not exist in the current university curriculum. I think NSA Centers of Academic Excellence program, for example, could be expanded, it’s something they currently operate jointly with DHS to include an OT cybersecurity focus and be able to really broaden university curriculum in this area.”
Rep. Mike Ezell (R-MS) questioned Clancy on the balance between risk and threat level across various sectors:
“Dr. Clancy, you raised a point about CISA needing to prioritize its efforts based on specific risks and threat levels for each sector. For example, the water sector may face more risks based on a historic lack of investment and expertise. On the other hand, the energy sector is more prone to threats from our adversaries…How do you believe CISA should navigate the balance between risk and threat considerations in the OT space?”
Clancy answered:
“I think where we see the adversaries focusing [are] these lifeline sectors, CISA has prioritized energy, water, telecommunications, and transportation as the four sectors that they think are the must-survive sectors with respect to critical infrastructure attacks. So I think we need to continue to prioritize those sectors, because without those sectors, the other sectors would see cascading failures.”

Subcommittee on Counterterrorism, Law Enforcement, and Intelligence Chairman August Pfluger (R-TX) asked witnesses to highlight differences between information technology and operational technology:
“Can you highlight a few key differences in the industrial cybersecurity community when it comes to different operational technologies?”
Lee answered:
“When you look at the operational technology side of the house, a lot of those IT security things that we know as basics and smart things to do are maybe not even the right emphasis. We talk about vulnerability management in IT, but we look at it from an intelligence perspective, it’s something like two or three percent of the vulnerabilities that matter to operational technology at all. So a lot of the time we just put the wrong emphasis on what we’re supposed to do with OT. We give out pages of guidance to folks that actually don’t move the needle towards operational resilience. If you steal from IT, you steal some data. You target OT, you kill people. You need to treat that differently.”
Rep. Pfluger continued:
“How can CISA improve their coordination and communication with EPA, the water industry, and the cyber community?”
Morley answered:
“They have made some substantial strides since the focus period of that report––starting with actually having a sector liaison dedicated to the water sector, which we didn’t really have for several years, so that’s a significant improvement in the Stakeholder Engagement Division. I think some of the current activities centered around elevating visibility and the vulnerability scanning service is a positive development, and we look forward to working to elevate the profile on how those resources can support utilities with some of these capacity challenges.”

Rep. Laurel Lee (R-FL) asked how CISA could accommodate smaller OT operators who need these cybersecurity tools:
“In your view, what can CISA do to make sure that the entities who can avail themselves of these tools and support know that they exist and actually engage in and utilize them?”
Morley answered:
“We’ve started some of those conversations, and I think what’s really important is the diversity and the complexity and capacity of the systems within the water sector really requires us to organize the resources in a manner that’s more accessible. Some of the resources that are there now are online––you don’t know what it is if you’re not a cyber expert; you’re not going to sign up for it. So I think a more collaborative effort with stakeholders to define different entry points into those resources, so it scales to what their need is, and then they progress within a maturity model, that would be very effective.”